Multilingual software isn’t a new idea. But it still matters when a specialized tool expands beyond English in a way that feels deliberate, polished, and genuinely useful.
All-About-PDF is the latest to make that move.
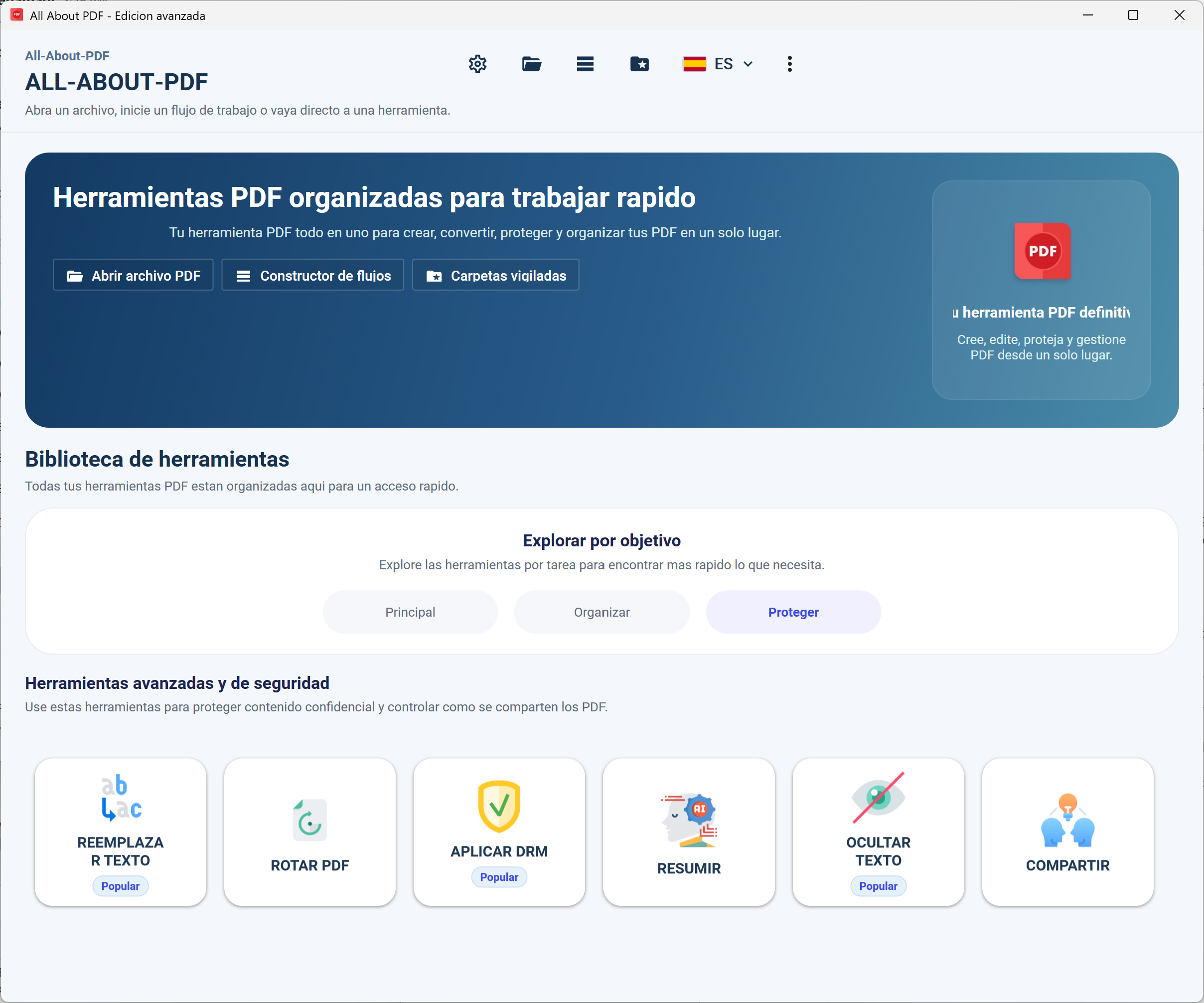
With its newest update, the PDF toolkit now supports Spanish, French, and German, opening the door for a much broader set of users to work with documents in a language that actually feels natural.
Less friction, more flow
If you’ve ever tried to process documents in a language that isn’t your own, you already know the problem. Even simple actions start to feel slower. Menus take longer to parse. Mistakes creep in.
That’s the friction multilingual support is meant to remove.
With this update, All-About-PDF’s interface, tools, and workflows adapt to your selected language, making everything from editing to automation feel more intuitive. It’s not a flashy feature, but it’s one that directly impacts how quickly and confidently you can get work done.
Not just translation — a more usable product
There’s a difference between software that’s technically translated and software that actually feels usable in another language.
This update leans toward the latter.
Multilingual support isn’t limited to a handful of labels or menus. It runs across the core experience — from navigation to processing tools to workflow automation. The idea is consistency. Once you switch languages, the entire app follows.
That matters more than it sounds, especially for teams.
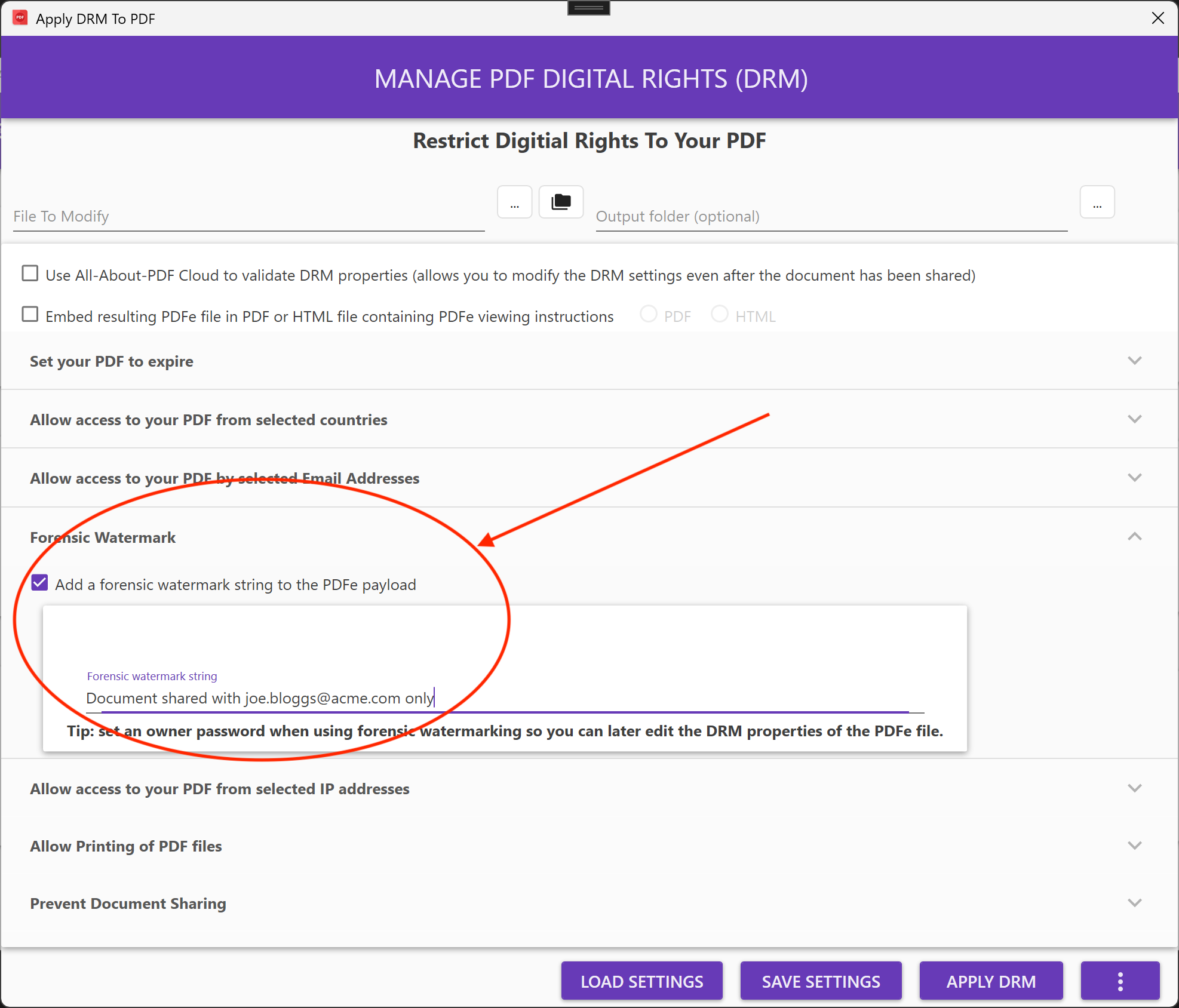
Built for how teams actually work
A lot of document workflows don’t live in one place anymore. Teams are spread across countries, time zones, and languages.
That’s where this kind of update starts to pull its weight.
Whether you’re sharing workflows, processing reports, or handling large batches of PDFs, being able to operate in your native language removes a layer of translation — both literal and mental. It makes collaboration smoother without forcing everyone into the same mold.
A small update with a bigger signal
On the surface, adding Spanish, French, and German might look like a routine feature update. But it points to something bigger.
Software is becoming more global by default.
And for tools like All-About-PDF — which already sit at the center of document-heavy workflows — that shift matters. The more accessible the tool, the more places it can realistically be used.
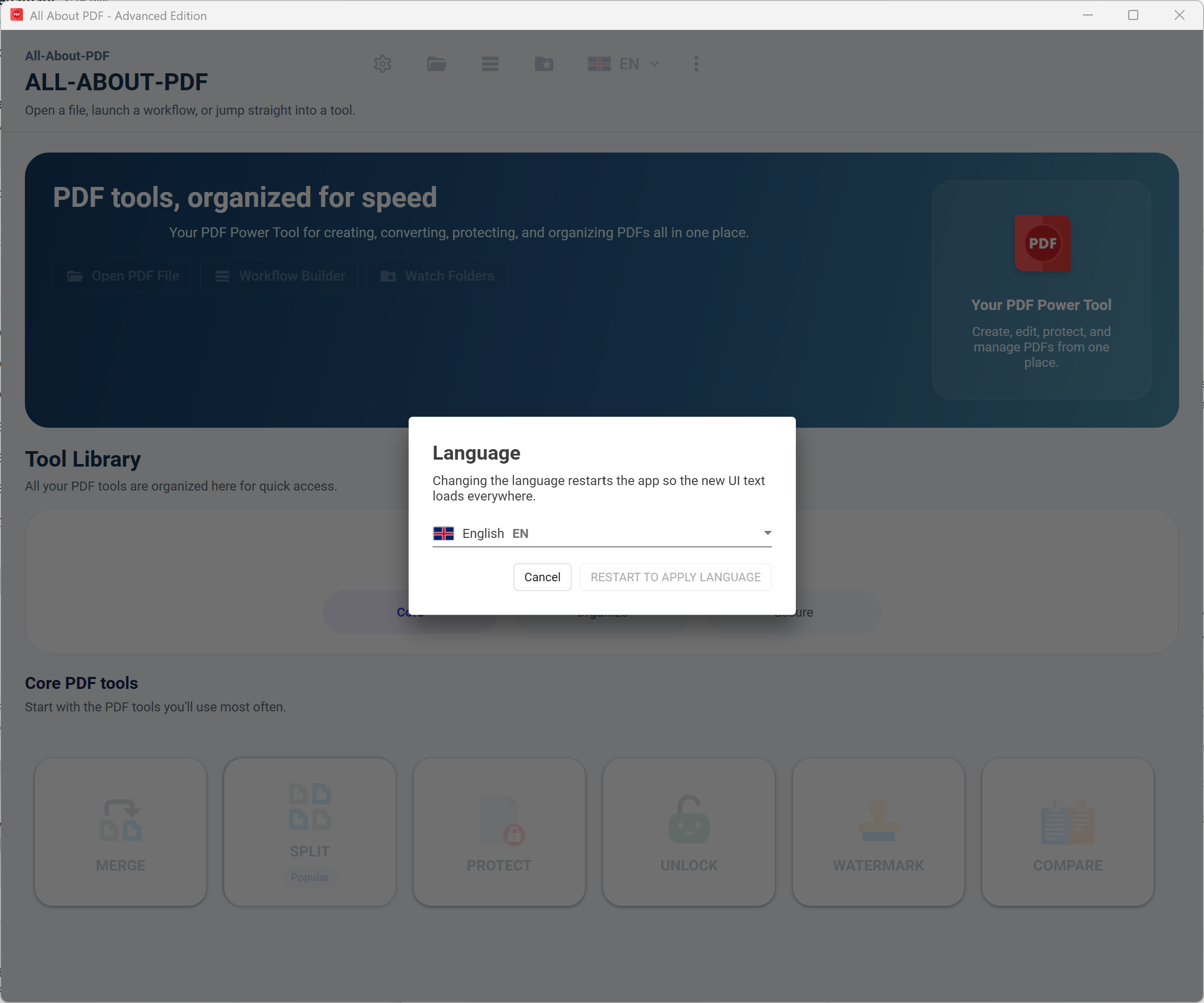
Switching is simple
If you’re already using All-About-PDF, switching languages takes a few clicks in the settings. No reinstall, no extra setup.
Pick your language, apply, and the interface updates after a restart of the application.
What’s next
This likely won’t be the end of it. Expanding language support tends to be iterative, and more options will follow.
For now, though, Spanish, French, and German are a solid start — and a clear step toward making the platform more accessible to a global audience.
Try it out
The latest version of All-About-PDF is available now, with full multilingual support built in.
If your workflow spans languages — or you simply prefer working in your own — this update makes a noticeable difference.