Most document leaks don't start with hackers.
They start with someone clicking forward.
An employee shares a PDF with a personal email to work from home. A partner sends a pricing sheet to someone they shouldn't. A customer redistributes a paid report to their entire team. A confidential document slowly spreads one "just sharing this with you" at a time.
And by the time the document surfaces somewhere it shouldn't be, one question always comes up:
Where did it come from?
For most organizations, the honest answer is: we have no idea.
That is why a security technique called forensic watermarking is starting to become a standard feature in modern document protection platforms.
Not because it prevents every leak.
But because it changes what happens after one.
Instead of trying to stop leaks, companies are making them traceable
Traditional document security has always focused on prevention:
- Passwords
- Encryption
- Permissions
- Access controls
These tools answer the question:
"Who should be allowed to open this?"
Forensic watermarking answers a different question:
"If this gets shared, can we trace who it came from?"
The idea is simple but powerful.
Every recipient gets a slightly different version of the same document. Not visually different in an obvious way, but structurally unique in ways that can later identify the source.
Sometimes this includes:
- Embedded identity markers
- Distribution metadata
- Recipient identifiers
- Timestamp fingerprints
- Invisible document signatures
Think of it like a digital fingerprint placed inside every copy.
If the file spreads, the fingerprint remains.
The real power isn't detection. It's behavior change.
Interestingly, the biggest benefit may not be catching leaks.
It may be preventing them in the first place.
Security experts sometimes call this deterrence through accountability. When people know something is traceable, they naturally become more careful.
It is the same reason body cameras change behavior.
Why audit logs reduce fraud.
Why visible cameras reduce theft.
Not because incidents never happen.
But because people know they can be identified if they do.
A simple notice that a document contains traceable identifiers can dramatically reduce unauthorized sharing.
Sometimes just knowing the technology exists is enough.
Where this shows up in the real world
This isn't theoretical. Forensic watermarking is already being used quietly across industries where PDFs are still the backbone of business communication.
Finance
Investment firms routinely distribute highly sensitive documents like forecasts, investor briefings, and acquisition plans.
If something leaks, the damage can be immediate.
With forensic watermarking, each distributed copy is tied to the recipient. If a document appears somewhere unexpected, the investigation becomes much shorter.
Software companies
Pricing documents are some of the most sensitive files software companies share.
If one partner leaks pricing:
- Negotiations become harder
- Discount expectations change
- Competitive positioning weakens
By uniquely marking each distributed document, companies gain visibility they previously didn't have.
Research firms
Anyone selling premium reports has faced the same problem:
One company buys a report.
That report gets shared internally.
Eventually it appears somewhere public.
Forensic watermarking allows sellers to identify which licensed copy became the source.
It doesn't just help enforcement.
It helps justify the business model.
HR and internal communications
Not all leaks go outside the company.
Some of the most damaging ones stay inside.
Salary changes. Restructuring plans. Investigation reports. These documents can spread quickly through internal networks if left unchecked.
Traceability adds a layer of accountability that internal policies alone often cannot.
Modern document security is becoming layered
No single feature solves document security anymore.
Instead, companies are combining multiple approaches:
Access control determines who can open a file.
Usage control determines what they can do with it.
Traceability determines what happens if it spreads.
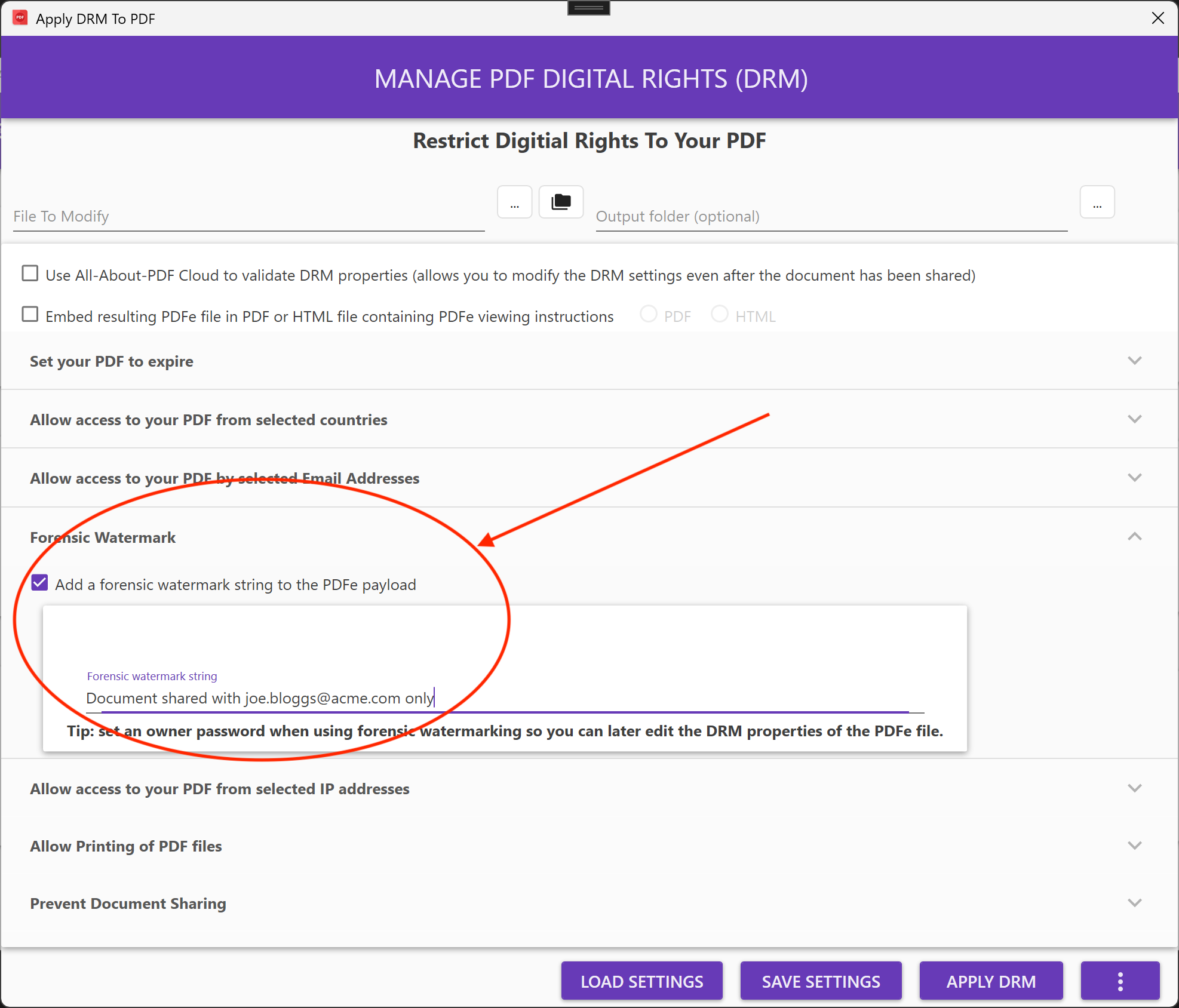
Platforms like All-About-PDF are part of this newer generation of tools that treat document security as a lifecycle rather than a lock.
Instead of just protecting the file at the moment it is opened, they focus on what happens throughout its existence.
That includes things like:
- Locking PDFs to verified identities
- Restricting access to specific devices
- Tracking document access events
- Applying expiration controls
- Embedding forensic identifiers
- Allowing document owners to revoke access
The goal isn't just protection.
It is control.
The uncomfortable reality companies are accepting
Organizations are starting to accept a difficult truth:
You cannot stop every leak.
Someone can always take a photo.
Someone can always retype information.
Someone can always share something manually.
What you can do is make leaks risky.
Forensic watermarking shifts the balance from blind trust to accountable trust.
Not "please don't share this."
But:
"If this gets shared, we will know where it came from."
That subtle shift is changing how companies think about document security.
Why this matters now
PDFs remain one of the most common ways sensitive information moves between organizations. Despite decades of digital transformation, critical business decisions still travel as attachments.
And attachments are easy to share.
As companies distribute more information across partners, customers, and remote teams, visibility after distribution is becoming just as important as protection before it.
That is where forensic watermarking fits.
Not as a dramatic new invention.
But as a quiet evolution in how organizations think about control.
Because increasingly, the question isn't:
"Can someone open this file?"
It is:
"What happens after they do?"